A study funded by the IMA® Research Foundation found that the nonprofit sector faces the whole range of financial fraud risks from theft of cash (showing the greatest number of incidents) to conflict of interest and falsification of financial statements (showing the highest average losses). The study suggests that the trusting environment found in many nonprofits, the lack of financial acumen at the top levels, and the failure to oversee financial matters in the same systematic manner as a commercial entity dramatically increase the potential for fraud. (For more, see Herbert Snyder, Margaret Andersen, and Jill Zuber, “Nonprofit Fraud: How Good Are Your Internal Controls?” , Strategic Finance, March 2017.)
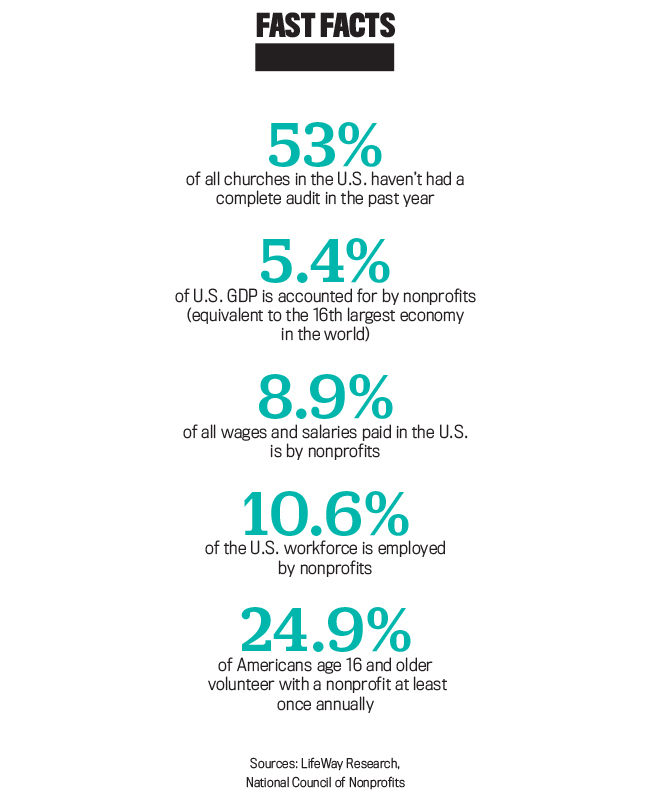
Despite this potential for harm, only one in six religious, charitable, and social services organizations in the 2018 ACFE study had performed a formal fraud risk assessment—a rate far lower than in the private sector—even though assessed risk usually drives required controls.
Yet the research also suggests that time-proven internal control concepts and techniques can reduce or eliminate the occurrence of fraud. Indeed, the ACFE reported in its 2018 survey that the presence of internal controls not only reduced fraud losses but also resulted in quicker fraud detection.
COSO’S IMPORTANT ROLE
As a recognized authority on internal controls and fraud deterrence, the Committee of Sponsoring Organizations of the Treadway Commission (COSO) offers an effective framework to safeguard nonprofit assets and deter fraud. Updated in 2013, the Internal Control—Integrated Framework has been used extensively by commercial entities to ensure they accomplish their business objectives. Some nonprofits have also found the structure and methods of COSO beneficial even though their environment isn’t business-oriented, but far fewer have taken advantage of this resource than organizations in the commercial sector.
The COSO Framework focuses on achieving operating, reporting, and compliance objectives through five control components—control environment, risk assessment, control activities, information and communication, and monitoring—along with 17 guiding principles that articulate the concepts that the components represent. If all five of the control components, and specifically the prin–ciples associated with each component, are functioning in an integrated manner, then the organization’s objectives ought to be achieved.
At the heart of the COSO Framework are the control components of risk assessment and control activities. Any event that could potentially get in the way of achieving an objective is considered a risk. Conversely, any action taken to manage a risk is considered a control. In short, controls mitigate risk and raise the odds that an objective will be achieved. An effective internal control system routinely identifies and analyzes risk and establishes controls based on the nature and extent of the assessed risk.
To illustrate, my parish’s food bank delivered surplus produce and baked and canned goods donated by local merchants to other food banks in the region. A downturn in the local economy (an external risk) would reduce the quantity of merchant donations, and the loss of volunteer drivers (an internal risk) would cut the number of food bank deliveries. Both risks, if they actually came to pass, would jeopardize surplus donations to other food banks, a key program objective.
PLUGGING THE HOLES
External risks by their nature are less controllable and therefore difficult to mitigate. Nonetheless, to control the risk during a local recession, our food bank could have published the names of contributing merchants in parish bulletins and flyers to generate community support for these businesses, as well as regularly solicited new merchants to grow the donor list, thereby mitigating the risk of insufficient donations during an economic downturn.
Internal risks are addressed more easily because the means to mitigate their impact generally fall within the purview of the organization. To control the risk of fewer volunteer drivers, the food bank might have established a procedure to solicit recently retired parishioners or young adults serving the parish in other capacities to help mitigate the risk.
While this approach might sound reasonable, the food bank was simply unfamiliar with the concept of assessing and controlling risk. As such, the risks, once realized, reduced the size and frequency of surplus donations to other food banks.
The core COSO control components—risk assessment and control activities—are likewise integral to the proper functioning of the other three components of an internal control system. Here’s why:
The control environment establishes the foundation of the internal control system by adding discipline and structure to the organization. For nonprofits, examples include governing boards, advisory bodies, codes of conduct, documented reporting lines, and a flow-down of authority and responsibility.
Information and communication support all other control components by communicating control responsibilities to employees (and volunteers, in the case of nonprofits), customers, and suppliers and by providing information in a form and time frame that allows them to carry out their duties. A good example would be letting a nonprofit supplier know in advance that deliveries won’t be accepted unless they’re accompanied by a copy of a purchase order.
Monitoring includes various types of audits and management reviews that determine whether the other control components are functioning as intended. For example, periodic inventories of parish-owned equipment and furniture, usually an audit procedure, would represent a monitoring control under COSO. If theft or misuse were detected, as it was in our parish after two backup power generators went missing, it would indicate a failure to assess risk properly and establish control activities effectively.
THE FINER POINTS OF RISK ASSESSMENT
Risk assessment isn’t well understood in the nonprofit sector and is therefore the most infrequently applied of all the COSO control components. By contrast, most commercial entities assess business risk in some form on a regular basis. If the assessment is formal, process flowcharts often will support risk identification, and complex matrices will help analyze and classify risk based on controls in place.
Flowcharts provide a picture of the process under study, showing the sequence of events and activities to achieve the process outcome, including the flow of documentation. Creating a flowchart would help all nonprofit stakeholders—governing board, finance council, paid staff, and volunteers—understand how responsibilities are assigned and how activities and documents are managed within a finance process. It also would encourage prompt discussion about where in the existing internal control structure the opportunity for fraud might be present.
The risks identified should be residual in nature. For example, inherent risk—the risk that exists in the absence of controls—would be at the maximum level for fraud in the absence of bank statement reconciliations, a control that helps identify check tampering or other forms of embezzlement. If reconciliations take place monthly, the risk likely will be reduced to a tolerable level. If the reconciliations are sporadic or rare, however, then, as a control, they’ll likely fail to achieve their intended purpose and instead create control risk. The following equation shows the relationship between residual risk, inherent risk, control, and control risk: Residual Risk = Inherent Risk – Control + Control Risk. Based on this equation, from this point forward we’ll assume that the risks identified for assessment are residual in nature.
ANALYZING AND CLASSIFYING RISK
Each identified risk is then analyzed into likelihood of occurrence and impact on operating performance. To facilitate the analysis, assume that each risk falls into one of the following three categories under likelihood and impact, respectively, and that operating conditions are normal.
LIKELIHOOD: What is the chance that the process risk will occur?
- Probable (high): quite likely to occur in time
- Possible (50/50): may occur at times
- Unlikely (low): not likely to occur but possible
IMPACT: What is the effect of the risk on process operations?
- Major (high): ongoing process existence is threatened
- Moderate (50/50): makes achieving some objectives problematic
- Minor (low): risk is manageable at a relatively routine level
A five-category scale also is common. For example, “certain” and “remote” might bookend the likelihood dimension, and “extreme” and “negligible” might do the same for the impact dimension.
Setting boundaries with as much granularity as possible helps reduce the subjectivity of the risk analysis. For example, likelihood could be expressed in time periods, depicting the expected number of risk occurrences per month, quarter, or year, while impact could be expressed in dollar amounts, showing a range of dollar losses per risk occurrence.
Nonprofits could review their own risks in a similar fashion, benchmarking themselves against other nonprofits with the same mission. Moreover, evaluating past nonprofit fraud events and brainstorming possible fraud scenarios with key nonprofit personnel also would help provide a basis for calculating likelihood and impact at the detail level. Ultimately, though, professional judgment will likely determine the final risk ratings, the same as it’s handled in the commercial sector.
CONSTRUCTING A RISK MATRIX
Next, likelihood and impact should be plotted on a risk assessment matrix comparable to Figure 1. The quadrants on the chart define different categories of risk based on the controls in place.
The combination of likelihood and impact determines the relative importance of assessed risk by quadrant. Each quadrant signals a different management approach to the risk at hand:
Critical risks (high likelihood, high impact) require strong, timely management controls to mitigate. For example, unfettered access to blank checks or a failure to define signature authority in the check-writing process leaves a nonprofit open to major fraud and the threat of insolvency. One of the more critical risks to a nonprofit is a failure to prepare a balanced budget and to review it periodically, leaving the entity open to budget overruns.
Difficult risks (low likelihood, high impact) are hard to manage because they occur so infrequently yet the adverse effect would be severe. For example, an accounting system breach could cause the loss of data needed to plan, organize, and control cash receipts and disbursements. For a nonprofit especially, substantial fraud could go undetected in the absence of such data.
Routine risks (high likelihood, low impact) are easier to manage because their incidence is generally controllable through existing processes. For example, while checks comprise the bulk of Sunday church collections, minor cash amounts also may be offered, providing an opportunity for theft during the collection process.
Low-importance risks (low likelihood, low impact) may only require ongoing monitoring to ensure they aren’t increasing in significance. For example, the chance of creating and paying fictitious employees in a small nonprofit is relatively low because everybody in the organization knows everybody else. For that reason, periodic monitoring of paycheck distribution normally would be sufficient to determine whether the payroll contains a fake employee.
A PLAN FOR MITIGATING RISK
Nonprofit and for-profit entities alike need to decide how to reduce the higher-importance risks to a lower, more tolerable level and whether to take action on risks of lesser importance. According to COSO, management responses to risk generally fall into one of four categories: avoiding, reducing, sharing, or accepting the risk.
Avoiding critical risks means ceasing the activity giving rise to the risk, such as closing a financially struggling nonprofit school because of low student enrollment and lack of funding. Reducing critical risks, on the other hand, requires implementing new or enhanced controls. For example, to mitigate the risk of check fraud, a church’s governing board could give the pastor the sole authority to sign checks and designate a clergy member as an emergency backup. Neither person, however, would be granted authority to access the accounting records or the blank checks, part of a segregation-of-duties policy.
For a church or small charity, reducing routine risks to control minor theft could involve tracking the amount of loose bills and change donated and then investigating differences from the historical trend over time.
Because of their size and often small staffs, nonprofits often need to share, transfer, or outsource a risk that may be unlikely but could have a huge impact on the organization’s solvency. Electronic information is a common risk area, due to the fact that the risk of a natural disaster or a data hack could cause a shutdown or breach of the organization’s accounting systems. In this case, a nonprofit could arrange incremental off-site backups, lowering its costs by copying only changes to the system data since the initial backup was performed.
Although it’s standard to accept certain risks, they need to be monitored to determine whether they’re becoming more significant over time. For example, prior to my involvement with the finance council of my church, the Sunday collections—which averaged $15,000 to $20,000 per week—had been kept overnight in an unlocked cabinet before being deposited the next day. An office assistant not only had access to the cash collections but also to the related cash and check listings, providing an opportunity for her to alter the records to conceal a theft.
Moreover, volunteer money counters tallied the cash and checks and prepared the listings, yet none of the counters had undergone a criminal background check, even though the archdiocese provided this service for a reasonable fee. There also were problems, since resolved, regarding the number of people who possessed keys to the building, thus giving them access to the unlocked cabinet. In short, too many people had keys who didn’t need them, and the parish building had never had its locks changed over the years. My top priority once I became involved was to correct the deficiencies in the Sunday collections process and then monitor the process going forward.
As soon as the control or management action for each risk response has been defined, the related cost, including resources and workload, will need to be estimated and assessed against the benefits to be derived from the risk mitigation. Is it reasonable and proportionate to the likelihood and impact involved? Does it satisfy the cost-benefit test?
APPLYING BEST PRACTICES TO NONPROFITS
As you can see, just a few documented controls, applied properly, will help nonprofits deter fraud, safeguard their assets, and maintain the propriety of their accounting records. None of these controls require a significant dollar investment, just time and attention to detail.
According to the ACFE, the most frequent cases of fraud in the nonprofit sector involved check tampering, billing schemes, or corruption (such as bribery and conflicts of interest). While a formal risk assessment will help ascertain the exact nature, timing, and extent of the controls needed, the following best practices, in combination, will serve to mitigate many obvious fraud risks.
- Create a robust COSO control environment by appointing an advisory board or a finance council to oversee fraud prevention. To help deter fraud, this entity should emphasize the importance of ethical behavior and adherence to internal controls at board, council, and staff meetings; establish written financial policies to be reviewed periodically by a credentialed (such as a CMA® (Certified Management Accountant) or CPA (Certified Public Accountant)) volunteer or employee of the nonprofit; and ensure background checks of all employees and volunteers who handle cash and conduct these checks periodically throughout the individuals’ employment or pro bono service—most embezzlers tend to be repeat offenders.
- Establish a segregation-of-duties policy to prevent the commingling of certain incompatible accounting functions: namely, transaction authorization, recording, and asset custody. Assigning more than one of these functions to the same person increases fraud risk.
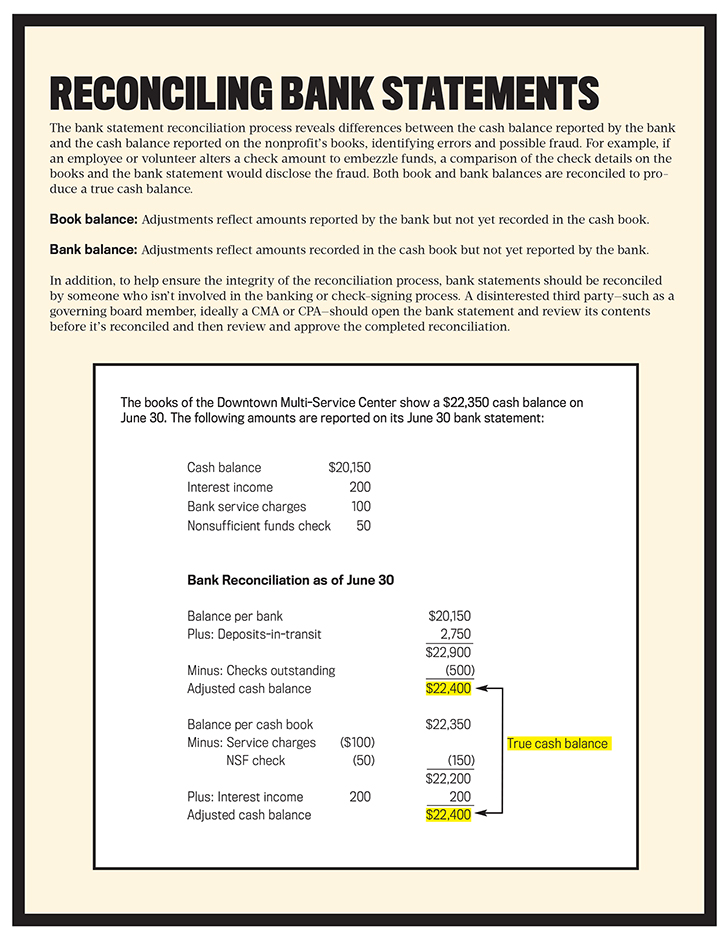
- Mandate monthly bank statement reconciliations to resolve differences between the cash balance reported by the bank and the cash balance reported on the nonprofit’s books. If a fraud has occurred, an investigation of the unreconciled differences should reveal it.
- Validate vendor and consultant invoices prior to check processing. This includes checking invoices to confirm that the goods were received in the quantities in which they were ordered and that all pricing is accurate; reviewing the math to ensure it’s correct; and establishing that each vendor is legitimate and not a fictitious company cooked up by someone inside or outside the organization to whom the payments would be funneled.
I’d recommend that all nonprofits engage the services of a CMA or CPA to examine, evaluate, and periodically review the internal control system to determine whether the components are operating as prescribed—a COSO monitoring requirement. That includes the best practices I’ve described. Likewise, an independent audit of the financial statement will help ferret out errors and fraud in nonprofit accounting systems and data. As a further precaution, reportable control conditions or material audit exceptions should be communicated to the nonprofit governing board. This should be done without staff present in order to encourage frank and open discussion between the board members and the accounting professionals.
Nonprofits that adopt a formal risk assessment based on COSO will align themselves with an authoritative professional standard for internal controls and fraud deterrence, offering assurance to donors that their dollars will be well-managed and used for the purposes they stipulate. While the path to adoption isn’t always navigated easily, nonprofits willing to make the journey—including yours, if you’re employed by or volunteer for one—will be rewarded by a stronger internal control system and a much lower risk of fraud.

May 2019